Many startups are examining the leaked code from the Wikileaks documents on the CIA’s hacking capabilities and already developing ways to protect something you might not think of when someone says “mobile device”: your car!
GGTN’s Mark Niu reports.

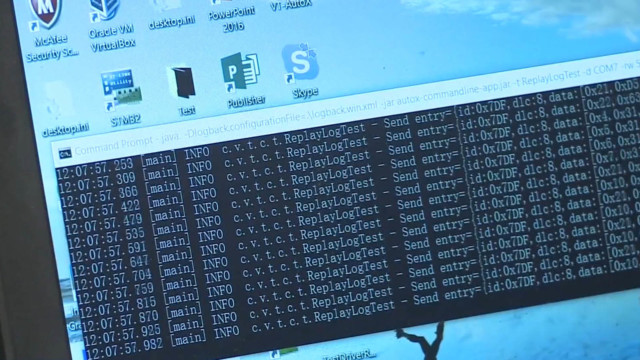
The Silicon Valley startup, Visual Threat, can simulate how to maliciously attack a car’s computer system and kill the engine.
Fortunately, the company has developed a solution for car manufacturers that is both firewall and anti-virus system to protect a vehicle.
The recent WikiLeaks dump of alleged C.I.A. documents claims the agency has looked into hacking cars to carry out assassinations that look like accidents
“It didn’t surprise me a lot, because when I read the articles. It looks to me that every vehicle have serious security problems. For example, we do the experiment before. We put a car into a certain status you can send any format of the message the car will stop. It’s very scary just imagine the autonomous driving yourself highway and people just control your vehicle remotely or put something in the OBD port when the next driver step in there may be some problem,” said Wei Yan, CEO & Founder, Visual Threat
WikiLeaks also claimed the C.I.A. could remotely turn on smartphone microphones and through “Operation Weeping Angel” — put a Samsung Smart TV in fake “off” mode, while it was secretly recording conversations.
Companies are beginning to hire hackers from all over the world to find security flaws in technology, including HackerOne.
“These are really tip of the spear attacks designed by CIA spies for targeting very hi-profile individuals. But technology is so commonplace that the methods used for those individuals could very easily be used for [edit] normal people, like I have a Samsung TV sitting in my bedroom and so I can empathize with what that feels like,” said Alex Rice, Co-Founder & CTO, HackerOne.
What surprises Rice most about the latest WikiLeaks document dump is how unprepared the CIA was despite earlier hacks of government agencies like the U.S. Office of Personal Management, OPM.
“It is absolutely a positive step that WikiLeaks is offering to share this information with defenders. The part is still an open question in my mind is it shouldn’t be a surprise to the CIA that an attack like this was possible, it happened to the NSA a few years ago, it’s happened to OPM, it’s happened to most tech companies at some point or another. So they should have been ready for what happens if our entire weapon arsenal leaks,” he said.
Rice is conflicted about the motives of WikiLeaks. While it may be in the public interest to know about the C.I.A.’s hacking methods, releasing the tools could make it possible for ordinary criminals – if not foreign governments – to use them.
 CGTN America
CGTN America